Choosing a managed detection and response partner is one of the higher-stakes decisions a security leader makes. You’re not buying a product. You’re handing someone ongoing access to your...


Choosing a managed detection and response partner is one of the higher-stakes decisions a security leader makes. You’re not buying a product. You’re handing someone ongoing access to your...

A concept called the "Post-Mythos era" has been making the rounds in security circles lately. The core argument is blunt: AI is accelerating the breakdown of assumptions traditional security programs...
Part 2 of 2: What a “Done” Sentinel Deployment Actually Looks Like: In Part 1 of this series, we walked through three specific problems SecureSky sees in almost every Sentinel environment we onboard:...

Part 1 of 2: What Failed SIEM Deployments Have in Common: When SecureSky onboards a new customer, one of the first things our team does is a thorough review of the Sentinel environment - what’s...

For small and medium-sized businesses (SMBs), the cybersecurity landscape has shifted dramatically. Threat actors no longer discriminate by company size; they target vulnerabilities wherever they...

In today’s digital-first world, LinkedIn has become a critical platform for professionals to network, share insights, and discover opportunities. But attackers are taking notice, and they’re using...
SecureSky has been named in the 2025 Frost Radar™ for Managed Detection and Response, recognized for pioneering the integration of Continuous Threat Exposure Management (CTEM) into traditional MDR...
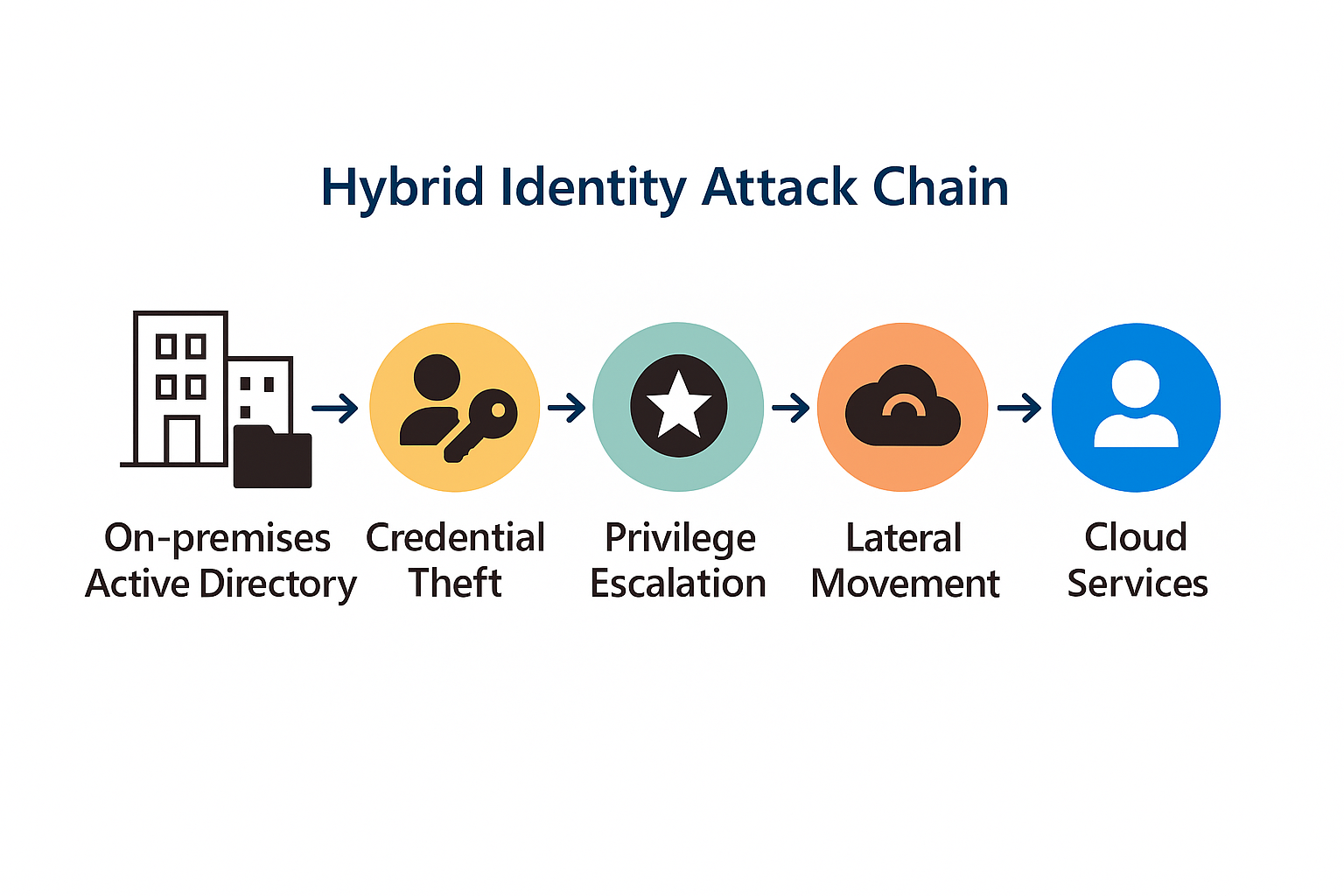
The move to the cloud has reshaped the cybersecurity landscape, shifting our focus to SaaS applications, cloud infrastructure, and the identities that access them. But for many organizations, the...

Ross Haleliuk’s recent post on Venture in Security offers one of the most comprehensive visualizations of cybersecurity consolidation to date. His breakdown shows how over 200 companies have merged,...

In today’s data-driven world, organizations are swimming in information—across clouds, apps, and platforms. Microsoft Purview offers a unified solution to help you discover, classify, protect, and...