Embrace Proactive CyberSecurity Solutions
Sep 11, 2023
In today's digital landscape, where a reported 75-80% of organizations face cyber attacks annually, the need for robust cybersecurity solutions has never been more critical. With the number of breaches rising, and the average cost of breaches increasing, companies are in danger more than ever of being the victim of a damaging breach that could cost millions of dollars and have a potentially long-lasting impact on the success of that organization.
The IBM 2023 Cost of a Data Breach Report states the average cost of a data breach reached an all-time high of USD 4.45 million, or $165 per record breached in 2023. This stark reality underscores the urgency for businesses to transition from traditional, reactive security approaches to more proactive, anticipatory strategies. The report, among others, also shows that times to identify and contain breaches have not improved over the past few years, despite all of the potential improvements in cybersecurity. The fact is that only about a third of attacks are identified by an organization’s security controls – the rest being identified by an uninvolved third party (like someone else saw your data online and contacted you), or by the attacker (like an attacker reaching out for a ransomware payment). That means most organizations are not even seeing 67% of breaches that affect them.
A significant factor in this is that most security programs have matured in a “watch and respond” mode, where you may have robust monitoring, but you are still reacting to something that already happened. A more proactive approach to cybersecurity can not only help you see what is happening right now but can also help you avoid potential attacks and compromises while anticipating those attacks.
The Path to Proactive Cybersecurity
The goal of proactive security is ultimately pretty straightforward – to improve your overall security program. Part of that goal includes the objectives of making proactive security uncomplicated, and doing so in a cost-effective manner.
A comprehensive proactive security solution does two things above all others.
- Has the goal of making you harder to attack. It does that primarily by improving your security posture – minimizing an attacker’s ability to exercise an attack that will be successful. Ongoing monitoring, threat hunting, and vulnerability management can reduce the vulnerabilities to which you are exposed, and help minimize the potential damage of a successful attack.
- Increases your ability to detect and manage a successful attack. This reduces your time to detect and improves your ability to respond in a meaningful and purposeful manner (reducing dwell time and reducing potential damage). If you can react faster and more effectively, you can reduce your exposure, and return to full operational capability more quickly.
To maximize your chances of successfully moving to a more proactive security posture, an MDR partner like SecureSky can be instrumental in developing and implementing a proactive security solution that meets your operational needs. SecureSky’s proactive managed security services are specifically designed to meet the needs of your proactive program.
Proactive Cybersecurity Protection
SecureSky’s proactive cybersecurity solution reduces an attacker’s ability to conduct a successful attack. Our team tests and enhances your existing configurations, reducing the chances an attacker can find exploitable configuration errors. We continually monitor your environment to help ensure that any configuration changes fit your organizational business and security goals and reduce the chances that a change can open you to new attacks. We identify exploitable vulnerabilities, and patching priorities to help reduce potential exposures. We provide advanced threat hunting to proactively identify and isolate threats that are not directly addressed by standard security solutions, and help develop advanced controls to eliminate or mitigate them. The entire goal of our threat exposure management solution is to minimize your attackable footprint, making it more difficult for attackers to find a viable avenue of attack. This approach helps you eliminate a significant amount of the attacks before you are even subjected to them, reducing the chances you will endure a successful attack, meaning you will be less likely to be one of the 75-80% of companies attacked every year.
Proactive MDR and SIEM Solutions
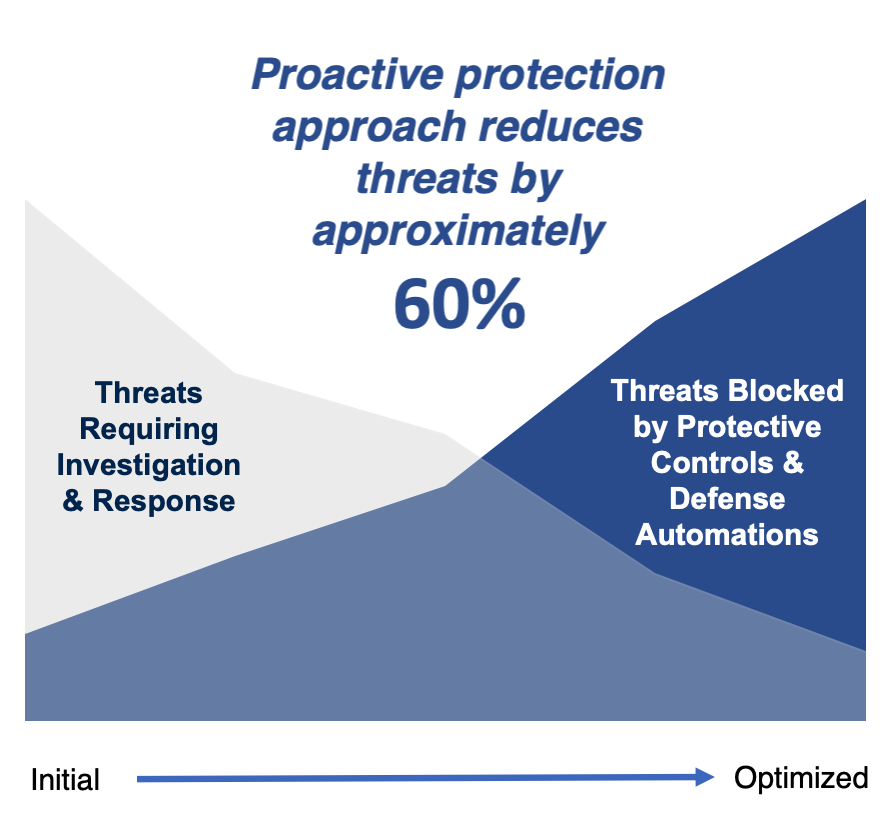
SecureSky also operates an effective managed detection and response solution. We provide advanced SIEM and XDR enablement, to help you actively manage the security-relevant information you consume. The SecureSky 2023 Mid-Year Azure Compliance Trends report shows that less than 50% of Microsoft XDR capabilities are used at all, much less effectively. Our consulting services help identify your most effective tool solution, remove redundancy (as well as cost and complexity), and help ensure the tools are providing the correct level and amount of data for your specific needs – right-sizing alerts to your needs and capabilities. Experience shows us that collaborating to establish an effective, proactive security program can reduce threats by approximately 60% from levels managed in a reactive security program. This approach means, that of the attacks you experience, you are increasing the chances that you will detect the attack above the standard 33% of attacks that are typically detected by an organization’s security program.
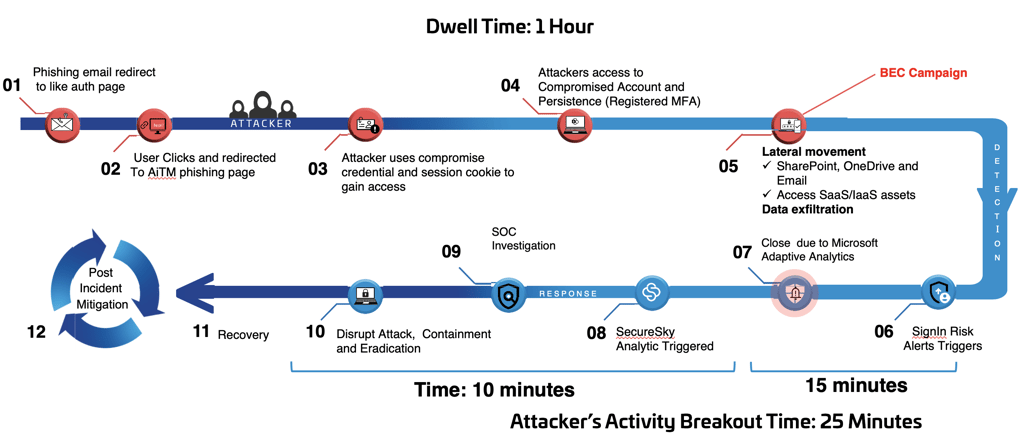
Our cybersecurity consulting services also help develop response and escalation procedures, as well as provide active incident response. Our services provide reporting proof for compliance initiatives, improving your ability to reliably and simply support audits and incident investigations. So, those attacks you do experience, you are better prepared to actively manage them. Adapting a more proactive process shrinks the dwell time of those attacks, meaning the attacker has less chance to fully infiltrate your environment and extract sensitive information, reducing the actual cost of a breach. The Mandiant M-Trends 2023 report states that dwell times for attackers – the number of days an attacker is present in a victim environment before being detected – fell to an all-time low of 16 days for 2022. However, by implementing an effective, proactive security program, SecureSky has seen this drop from weeks to minutes.
Optimizing Your Cybersecurity Landscape
SecureSky’s solutions are explicitly designed and implemented to simplify your operations and maximize your control over your security-relevant data. This includes reducing your attackable footprint and then helping you actively maintain that smaller footprint. It also includes maximizing the effectiveness of your security-spend, by making the best use of available tools and providing information your security and business decision-makers can use to best support your business.
Embracing a proactive security solution starts with the decision, and is followed by a journey. But the destination is a security posture that helps you to significantly mitigate the impact of cyber threats, improve uptime, protect your reputation, and consistently enable your business needs with proper levels of security.
