Will Coronavirus Impact Cybersecurity Operations?
Mar 5, 2020
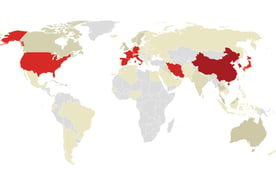
In 2020, coronavirus dominated headlines worldwide, with governments and healthcare systems grappling to manage and mitigate its spread. Amidst this uncertainty, questions arise about its potential to become an epidemic or pandemic, the speed at which treatments will emerge, and its overall impact on global health and productivity. This situation also casts a spotlight on the resilience of cybersecurity operations, underscoring the importance of robust cybersecurity services, including Managed Detection and Response (MDR), in navigating these challenging times.
Navigating Cybersecurity Challenges Amidst the Coronavirus Crisis
As the world grapples with the coronavirus outbreak, businesses are taking unprecedented steps, including enhancing prevention awareness, imposing travel restrictions, and transitioning major events to digital platforms. This period of uncertainty has prompted a thorough review of disaster recovery and business continuity plans, especially as companies face potential workforce shortages and supply chain disruptions.
For cybersecurity operations, the current situation demands an equally proactive approach. Leadership must consider not only the direct impacts, such as employee illness and hardware shortages but also less apparent challenges:
- Third-Party Support Vulnerabilities: Illness among employees at essential third-party services, including outsourced help desks, identity and access management, maintenance vendors, Managed Service Providers (MSPs), or Managed Security Service Providers (MSSPs), could compromise security operations.
- Economic Downturn Preparations: The need for strategic planning in the face of possible budget cuts due to an economic downturn.
- Increased Phishing Risks: The unfortunate reality is that crises like the coronavirus can spur phishing activities, leading to potential ransomware/malware attacks, account takeovers, and subsequent financial and reputational damage.
To mitigate these risks, SecureSky recommends incorporating several key elements into your cybersecurity strategy:
- Remote Operation Capabilities: For Security Operations Centers (SOCs) reliant on desktops, assess the need for laptops or mobile devices to maintain essential cybersecurity services, including risk prevention, threat detection, response, and support functions.
- Alternative Communication Strategies: If relying on corporate telecommunication infrastructure, explore backup mobile communication options, such as procuring mobile phones or leveraging employee-owned devices, with clear reimbursement policies.
- Remote Work Testing: Conduct comprehensive tests of remote work scenarios to ensure seamless access, authentication processes, and the capacity of VPN and web conferencing tools.
- Vendor Continuity Planning: Understand the disaster recovery and business continuity plans of mission-critical vendors, ensuring they are prepared for COVID-19 and similar crises.
- Automation with SOAR and SIEM: Leverage Security Orchestration, Automation, and Response (SOAR), and Security Information and Event Management (SIEM) tools to automate routine cybersecurity tasks, preparing for reduced staff availability.
- Phishing Prevention Controls: Implement and enhance email phishing prevention measures and educate employees on recognizing scam attempts.
- Security Awareness Reinforcement: Emphasize the importance of security awareness, particularly regarding coronavirus-related scams and phishing attacks.
As we navigate these challenging times, SecureSky extends its support to those affected by the coronavirus and commends the efforts of healthcare professionals worldwide. Our guidance aims to prepare organizations for a range of disaster scenarios, emphasizing the critical role of cybersecurity services, including managed detection and response, in ensuring operational resilience. Planning for the worst while hoping for the best is prudent, and SecureSky is here to assist in fortifying your cybersecurity posture.
